The goal of this project is to find out the fake access points opened by the WiFi pineapple device using the PineAP module and to prevent clients from being affected by initiating a deauthentication attack to the attacking device.
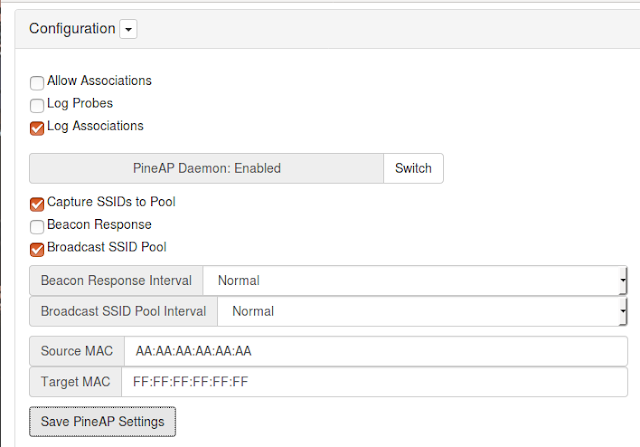
How PineAP Module Works
- Collects SSID information
- Creates SSID pool with collected SSID information
- Creates fake access points using information in the SSID pool
Where is the problem?
One MAC address, more than one SSID information .... ..- -. - . .-.
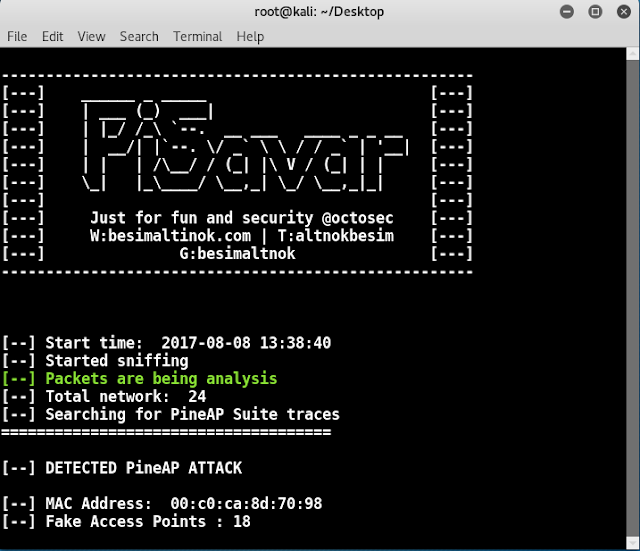
Features of PiSavar
- Detects PineAP activities
- Detects networks opened by PineAP.
- Starts deauthentication attack for PineAP.
Features to add
- List of clients connected to fake access points
- Record activities - Logging
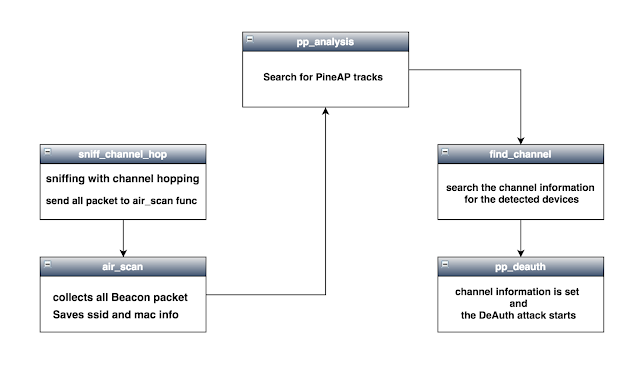
Diagram
Usage
Requirements
- Hardware: TP LINK TL-WN722N
- Modules: scapy, time, termcolor, sys
Kali Linux:
Download pisavar:
git clone https://github.com/besimaltnok/PiSavar.gitInstall Python librarie(s):
pip install termcolorIt's done!
Run the program with following command:
Monitor mode:
airmon-ng start interface(wlan0,wlan1) (Monitor mode)
or
ifconfig wlan0 down
iwconfig wlan0 mode Monitor
ifconfig wlan0 upcd PiSavar
python pisavar.py wlan0monScreenshots
Demo Video
Authors
This project is coded by Besim ALTINOK