Netsparker Web Application Security Scanner can find and report web application vulnerabilities such as SQL Injection and Cross-site Scripting (XSS) and security issues on all web applications and websites regardless of the platform and the technology they are built on.
Netsparker is very easy to use and its unique detection and safe exploitation techniques allow it to be dead accurate in reporting hence it is the first and only False Positive Free web vulnerability scanner, therefore users can focus on remediating reported vulnerabilities and security issues without wasting time on learning how to use the web vulnerability scanner or verify its findings.
Changelog - 3.5.3
NEW FEATURES
* DOM based cross-site scripting vulnerability scanning* Chrome based web browser engine for DOM parsing
* URL rewrite rules configuration wizard (to scan parameters in URLs)
* "Ignore Vulnerability from Scan" option to exclude vulnerabilities from reports
NEW SECURITY TESTS
* Nginx web server Out-of-date version check* Perl possible source code disclosure
* Python possible source code disclosure
* Ruby possible source code disclosure
* Java possible source code disclosure
* Nginx Web Server identification
* Apache Web Server identification
* Java stack trace disclosure
IMPROVEMENTS
* Improved the correctness and coverage of Remote Code Execution via Local File Inclusion vulnerabilities* Improved cross-site scripting vulnerability confirmation patterns
* Added support for viewing JSON arrays in document roots in request/response viewers
* Added support for Microsoft Office ACCDB database file detection
* Improved DOM parser to exclude non-HTML files
* Improved PHP Source Code Disclosure vulnerability detection
* Improved Nginx Version Disclosure vulnerability template
* Improved IIS 8 Default Page detection
* Improved Email List knowledgebase report to include generic email addresses
* Improved Configure Form Authentication wizard by replacing embedded record browser with a Chrome based browser
* Improved the form authentication configuration wizard to handle cases where Basic/NTLM/Digest is used in conjunction with Form Authentication
* Added a cross-site scripting attack pattern which constructs a valid XHTML in order to trigger the XSS
* Added double encoded attack groups in order to reduce local file inclusion vulnerability confirmation requests
* Added status bar label which displays current VDB version and VDB version update notifications
* Added login activity indicator to Scan Summary Dashboard
* Added a new knowledgebase out-of-scope reason for links which exceed maximum depth
* Updated external references in cross-site scripting vulnerability templates
* Improved DOM parser by providing current cookies and referer to DOM/JavaScript context
* Added several new DOM events to simulate including keyboard events
* Improved the parsing of "Anti-CSRF token field names" setting by trimming each individual token name pattern
* Added support for simulating DOM events inside HTML frames/iframes
* Consolidated XSS exploitation function name (netsparker()) throughout all the areas reported
* Removed redundant semicolon followed by waitfor delay statements from time based SQLi attack patterns to bypass more blacklistings
* Changed default user-agent string to mimic a Chrome based browser
* Improved LFI extraction file list to extract files from target system according to detected OS
* Removed outdated PCI 1.2 classifications
FIXES
* Fixed indentation problem of bullets in knowledgebase reports* Fixed path disclosure reports in MooTools JavaScript file
* Fixed KeyNotFoundException occurs when a node from Sitemap tree is clicked
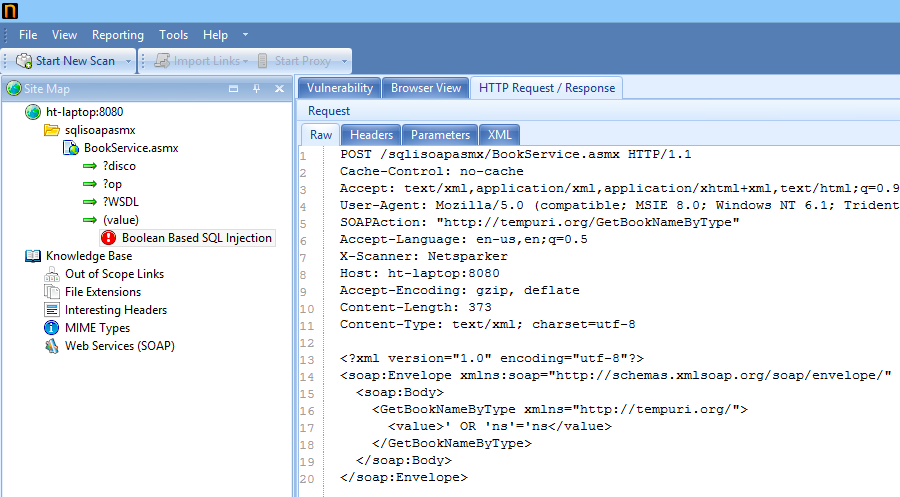
* Fixed NullReferenceException thrown from Boolean SQL Injection Engine
* Fixed an issue in WebDav Engine where an extra parameter is added when requesting with Options method
* Fixed a bug where LFI exploitation does not work for double encoded paths
* Fixed a bug in Export file dialog where .nss extension isn't appended if file name ends with a known file extension
* Fixed a bug in Configure Form Authentication wizard where the number of scripts loaded shows incorrectly
* Fixed a bug which occurs while retesting with CSRF engine
* Fixed a bug where retest does not work after loading a saved scan session
* Fixed a bug where Netsparker reports out of date PHP even though PHP is up to date
* Fixed a UI hang where Netsparker tries to display a binary response in Browser View tab
* Fixed an ArgumentNullException thrown when clicking Heartbleed vulnerability
* Fixed a bug where Netsparker makes requests to DTD URIs in XML documents
* Fixed a bug in Scan Policy settings dialog where list of user agents are duplicated
* Fixed a typo in ViewState MAC Not Enabled vulnerability template
* Fixed a bug in auto updater where the updater doesn't honour the AutoPilot and Silent command line switches
* Fixed XSS exploit generation code to handle cases where input name is "submit"
* Fixed a bug that prevents Netsparker.exe process from closing if you try to close Netsparker immediately after starting a new scan
* Fixed a UI hang happens when the highlighted text is huge in response source code
* Fixed issues with decoded HTML attribute values in text parser
* Fixed session cookie path issues according to how they are implemented in modern browsers
* Fixed scan stuck at re-crawling issue for imported scan sessions
* Fixed highlighting issues for possible XSS vulnerabilities
* Fixed a crash due to empty/missing URL value for form authentication macro requests
* Fixed a NullReferenceException in Open Redirect Engine which occurs if redirect response is missing Location header
* Fixed an error in authentication macro sequence player happens when the request URI is wrong or missing